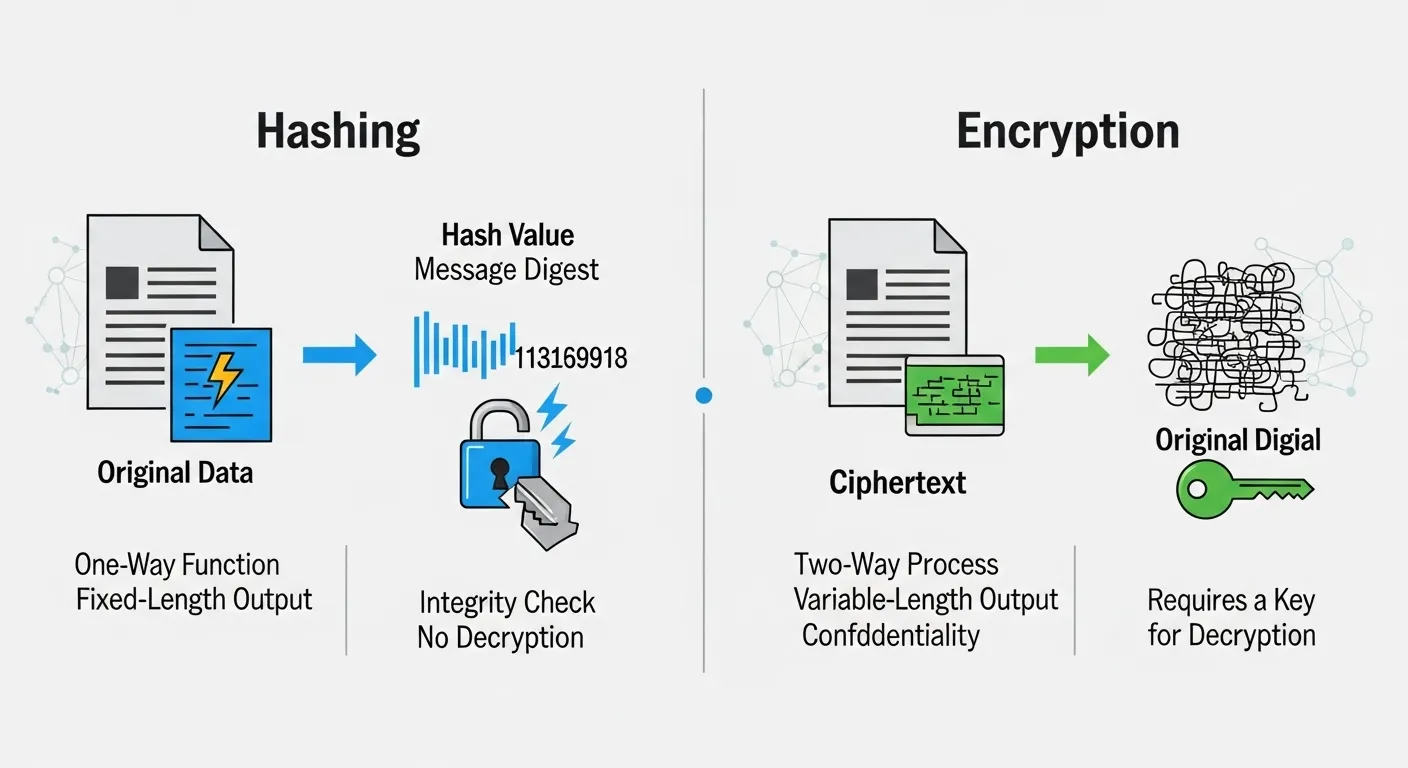
When Ayesha signed up for a new app, she noticed it asked for a password but never showed it again, even the company couldn’t retrieve it. Meanwhile, when she sent a private message, it was securely transmitted and could be read only by the receiver. These two everyday scenarios highlight the difference between hashing and encryption. While both are used to protect data, the difference between hashing and encryption lies in how they process and secure information. Understanding the difference between hashing and encryption is essential in today’s digital world, where data privacy is critical. In fact, the difference between hashing and encryption determines whether data can be reversed or not, making it vital for cybersecurity, authentication, and secure communication.
Key Difference Between the Two
The main difference between hashing and encryption is:
- Hashing is a one-way process; data cannot be converted back to its original form.
- Encryption is a two-way process data can be decrypted back using a key.
Why is the difference important to know?
Understanding the difference between hashing and encryption is crucial for developers, IT professionals, and everyday users. It helps in choosing the right method for securing passwords, messages, and sensitive data. In society, the proper use of these techniques ensures safe online transactions, secure communication, and protection against cyber threats. For experts, this knowledge is the foundation of modern cybersecurity systems.
Pronunciation (US & UK)
- Hashing
- US: /ˈhæʃɪŋ/
- UK: /ˈhæʃɪŋ/
- Encryption
- US: /ɪnˈkrɪpʃən/
- UK: /ɪnˈkrɪpʃən/
Linking Hook
Now that you understand the basics, let’s explore the detailed difference between hashing and encryption with practical examples.
H2: Difference Between Hashing and Encryption
1. Nature of Process
- Hashing: One-way transformation.
- Example 1: Password stored as a hash.
- Example 2: Cannot retrieve original password.
- Encryption: Two-way transformation.
- Example 1: Message encrypted before sending.
- Example 2: Receiver decrypts it.
2. Purpose
- Hashing: Data integrity and verification.
- Example 1: Checking file authenticity.
- Example 2: Password storage.
- Encryption: Data confidentiality.
- Example 1: Secure emails.
- Example 2: Online banking transactions.
3. Reversibility
- Hashing: Irreversible.
- Example 1: Cannot decode hash.
- Example 2: Only compared, not reversed.
- Encryption: Reversible with key.
- Example 1: Decryption restores original text.
- Example 2: Requires secret key.
4. Key Usage
- Hashing: No key required.
- Example 1: Uses algorithms like SHA.
- Example 2: Same input gives same output.
- Encryption: Uses keys (public/private).
- Example 1: AES encryption key.
- Example 2: RSA key pair.
5. Output
- Hashing: Fixed-length output.
- Example 1: SHA-256 always same length.
- Example 2: Short digest of data.
- Encryption: Variable-length output.
- Example 1: Depends on input size.
- Example 2: Encrypted text length varies.
6. Speed
- Hashing: Faster.
- Example 1: Quick password checks.
- Example 2: Efficient for large data.
- Encryption: Slower.
- Example 1: Requires complex algorithms.
- Example 2: Needs key processing.
7. Use Cases
- Hashing: Passwords, checksums.
- Example 1: Login systems.
- Example 2: File verification.
- Encryption: Secure communication.
- Example 1: HTTPS websites.
- Example 2: Messaging apps.
8. Security Focus
- Hashing: Prevents tampering.
- Example 1: Detects data changes.
- Example 2: Ensures integrity.
- Encryption: Prevents unauthorized access.
- Example 1: Protects sensitive data.
- Example 2: Keeps messages private.
9. Algorithms
- Hashing: SHA-256, MD5.
- Example 1: Used in blockchain.
- Example 2: Digital signatures.
- Encryption: AES, RSA.
- Example 1: Used in SSL/TLS.
- Example 2: Secure file storage.
10. Data Recovery
- Hashing: Not possible.
- Example 1: Lost password cannot be retrieved.
- Example 2: Must reset password.
- Encryption: Possible with key.
- Example 1: Decrypt encrypted file.
- Example 2: Recover original message.
Nature and Behaviour
- Hashing: Deterministic, irreversible, and integrity-focused.
- Encryption: Secure, reversible, and confidentiality-focused.
Why People Are Confused?
Both hashing and encryption are used for data security, so people often assume they are the same. Their technical nature and similar usage contexts also add to the confusion.
Comparison Table
| Feature | Hashing | Encryption | Similarity |
| Process | One-way | Two-way | Protect data |
| Purpose | Integrity | Confidentiality | Security |
| Reversibility | No | Yes | Use algorithms |
| Key | Not required | Required | Used in cybersecurity |
| Output | Fixed length | Variable length | Transform data |
Which Is Better in What Situation?
Hashing is better when you need to store sensitive data like passwords securely without ever needing to retrieve the original value. It is ideal for authentication and data integrity checks.
Encryption is better when you need to send or store data securely but still need to access it later. It is essential for communication, file protection, and secure transactions.
Metaphors and Similes
- Hashing: “Like turning a document into a unique fingerprint.”
- Encryption: “Like locking a message in a box with a key.”
Connotative Meanings
- Hashing: Neutral (secure and final)
- Encryption: Positive (protective and flexible)
Idioms and Proverbs (Creative Use)
- “Set in stone” → Hashing
- “Lock and key” → Encryption
Works in Literature
- Cybersecurity textbooks and cryptography research papers (various authors)
Movies Related to the Topic
- “The Imitation Game” – 2014, UK/USA
- “Blackhat” – 2015, USA
FAQs
1. Can hashing be reversed?
No, hashing is irreversible.
2. Why is encryption reversible?
Because it uses keys for decryption.
3. Which is more secure?
Both are secure but used for different purposes.
4. Is hashing used in passwords?
Yes, passwords are stored as hashes.
5. Can they be used together?
Yes, systems often use both for maximum security.
How Both Are Useful for Society
Hashing and encryption protect personal data, secure online transactions, and ensure privacy in communication, making the digital world safer.
Final Words for Both
Hashing and encryption are essential tools in modern cybersecurity, each serving a unique and critical role.
Conclusion
In conclusion, the difference between hashing and encryption lies in their reversibility, purpose, and application. Hashing is a one-way process used for integrity and authentication, while encryption is a two-way process used for confidentiality and secure communication. Understanding the difference between hashing and encryption helps individuals and professionals make better decisions in protecting digital information in an increasingly connected world.